Description
Introduction
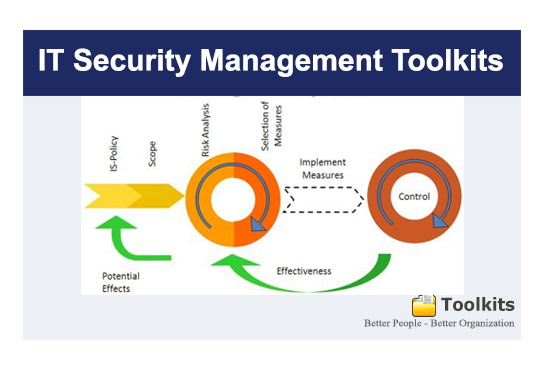
Information security programs protect the confidentiality, integrity, and availability of data and information technology assets in enterprise. IT Manager or CIO must understand legal obligations, standard practices, and technology basics to meet business needs in this rapidly changing area.
Nowadays, with the digitalization of our society, the need for data protection became more important. The latest IT Security Standards involve the application of technology to broader social and institutional contexts, and thereby contributes to the servitization of companies, and affects how they compete and interact.
This document contains security technology solutions to protect data classified as ‘Highly Sensitive’, ‘Sensitive’, ‘Private’ or ‘Public’ as per the Data Classification Standard and Data Handling Guidelines.
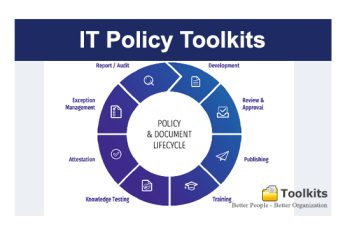
Download this IT Security Kit now and get direct access to newly updated IT Security Kit Standard templates, including policies, controls, processes, checklists, procedures and other documents.
Template Toolkits Name
Part-1. IT Security Standards & Checklists
CIO-SEC01.Account Management Standard.doc
CIO-SEC02.Account Management Checklist.doc
CIO-SEC03.Desktop and Portable Computer Standard.doc
CIO-SEC04.Desktop and Portable Computer Standard System Admins Checklist.doc
CIO-SEC05.Password Standard.doc
CIO-SEC06.Portable Media Standard.doc
CIO-SEC07.Information Access and Protection.doc
CIO-SEC08.Information Access and Protection Inventory Template.doc
CIO-SEC09.Information Access and Protection Questionnaire.doc
CIO-SEC10.Network Security Standard.doc
CIO-SEC11.Network Security Checklist.doc
CIO-SEC12.Server Security Standard.doc
CIO-SEC13.ServerSecurityChecklist.doc
CIO-SEC14.ServerSecurityChecklist.xls
CIO-SEC15.Signature Standard.doc
CIO-SEC16.Web Security Standard.doc
CIO-SEC17.Web Standard Compliance Checklist.doc
CIO-SEC18.Storage Media Disposal.doc
CIO-SEC19.Solutions Life Cycle Management.doc
CIO-SEC20.Security Incident Handling Standard.doc
CIO-SEC21.Incident Handling Flowchart.doc
CIO-SEC22. Disaster Recovery.doc
CIO-SEC23.Non Disclosure Agreement (NDA).doc
CIO-SEC24. Systems Support Personnel Non Disclosure Agreement.doc
Part-2. IT Security Policies
CIO-SEC01.Acceptable Encryption Policy.doc
CIO-SEC02.Acceptable Use Policy.doc
CIO-SEC03.Acquisition Assessment Policy.doc
CIO-SEC04.Analog/ISDN Line Security Policy.doc
CIO-SEC05.Anti-Virus Guidelines.doc
CIO-SEC05.Automatically Forwarded Email Policy.doc
CIO-RK07.Bluetooth Baseline Requirements Policy.doc
CIO-SEC08.Clean Desk Policy.doc
CIO-SEC09.Communications Equipment Policy.doc
CIO-SEC10.Data Breach Response Policy.doc
CIO-SEC11.Database Credentials Policy.doc
CIO-SEC12.Dial In Access Policy.doc
CIO-SEC13.Digital Signature Acceptance Policy.doc
CIO-SEC14.Disaster Recovery Plan Policy.doc
CIO-SEC15.DMZ Lab Security Policy.doc
CIO-SEC16.Email Policy.doc
CIO-SEC17.Email Retention Policy.doc
CIO-SEC18.Employee Internet Use Monitoring and Filtering Policy.doc
CIO-SEC19.End User Encryption Key Protection Plan.doc
CIO-SEC20.Ethics Policy.doc
CIO-SEC21.Extranet Policy.doc
CIO-SEC22.Incident Handling – Chain Of Custody Form.doc
CIO-SEC23.Incident Handling Forms – Incident Communication Log.doc
CIO-SEC24.Incident Handling Forms – Incident Contacts List.doc
CIO-SEC25.Incident Handling Forms – Incident Containment.doc
CIO-SEC25.Incident Handling Forms – Incident Eradication.doc
CIO-SEC27.Incident Handling Forms – Incident Identification.doc
CIO-SEC28.Incident Handling Forms – Incident Survey.doc
CIO-SEC29.Information Logging Standard.doc
CIO-SEC30.Intellectual Property Incident Handling Forms – Incident Communication Log.doc
CIO-SEC31.Intellectual Property Incident Handling Forms – Incident Contacts.doc
CIO-SEC32.Intellectual Property Incident Handling Forms – Incident Containment.doc
CIO-SEC33.Intellectual Property Incident Handling Forms – Incident Eradication.doc
CIO-SEC34.Intellectual Property Incident Handling Forms – Incident Form Checklist.doc
CIO-SEC35.Intellectual Property Incident Handling Forms – Incident Identification.doc
CIO-SEC36.Internet DMZ Equipment Policy.doc
CIO-SEC37.Internet Usage Policy.doc
CIO-SEC38.Lab Anti Virus Policy.doc
CIO-SEC39.Lab Security Policy.doc
CIO-SEC40.Mobile Device Encryption Policy.doc
CIO-SEC41.Mobile Employee Endpoint Responsibility Policy.doc
CIO-SEC42.Pandemic Response Planning Policy.doc
CIO-SEC43.Password Construction Guidelines.doc
CIO-SEC44.Password Protection Policy.doc
CIO-SEC45.Personal Communication Devices and Voicemail Policy.doc
CIO-SEC46.Remote Access Mobile Computing Storage.doc
CIO-SEC47.Remote Access Policy.doc
CIO-SEC48.Remote Access Tools Policy.doc
CIO-SEC49.Removable Media Policy.doc
CIO-SEC50.Risk Assessment Policy.doc
CIO-SEC51.Router and Switch Security Policy.doc
CIO-SEC52.Security Response Plan Policy.doc
CIO-SEC53.Server Audit Policy.doc
CIO-SEC54.Server Malware Protection Policy.doc
CIO-SEC55.Server Security Policy.doc
CIO-SEC56.Social Engineering Awareness Policy.doc
CIO-SEC57.Software Installation Policy.doc
CIO-SEC58.Technology Equipment Disposal Policy.doc
CIO-SEC59.Virtual Private Network Policy.doc
CIO-SEC60.Web Application Security Policy.doc
CIO-SEC61.Wireless Communication Policy.doc
CIO-SEC62.Wireless Communication Standard.doc
CIO-SEC63.Workstation Security (For HIPAA) Policy.doc





kliens
January 2, 2022IT toolkit has REVOLUTIONIZED our IT, It forms the bedrock of our SOP toolkit, enables us to generate run books and has dramatically lowered the cost of training new IT staff, while increasing user’s satisfation.
henrietta
January 2, 2022Once we implemented IT Toolkit, all of that changed. Now we have an IT final plan that looks professional, is well organized and makes it easy for everyone to find the information that they need.